System & Data Security

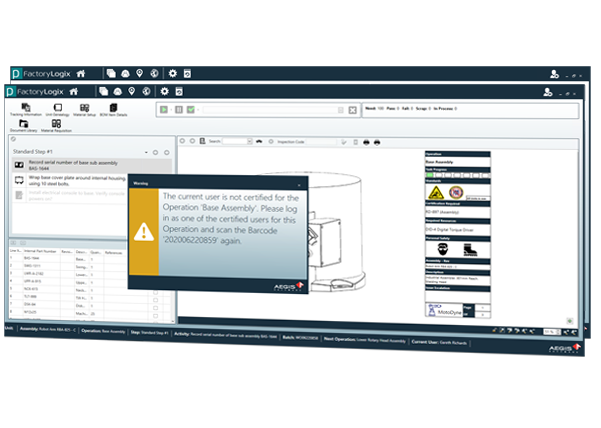
Critical steps audit
At key operations, the data clearance portal is used.

Active defensive attack
The system can defend against common attacks such as XSS, CSRF, SQL injections and DDOS.

Sensitive data encryption
Encrypted storage for sensitive data, for communicationsServices, sensitive interfaces are also encrypted.
Controlling costs, ensuring product quality and simplifying compliance.

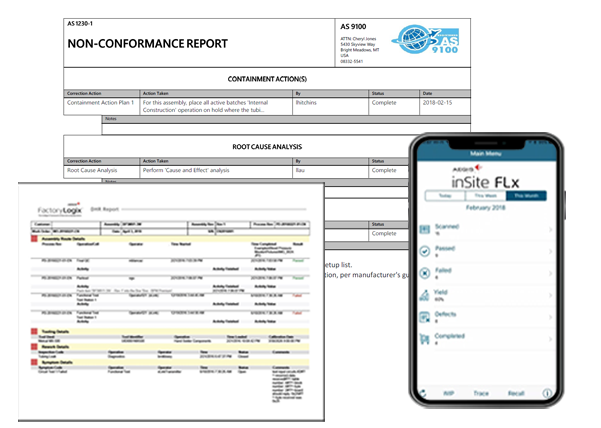
Risk reduction

Promoting continuous improvement

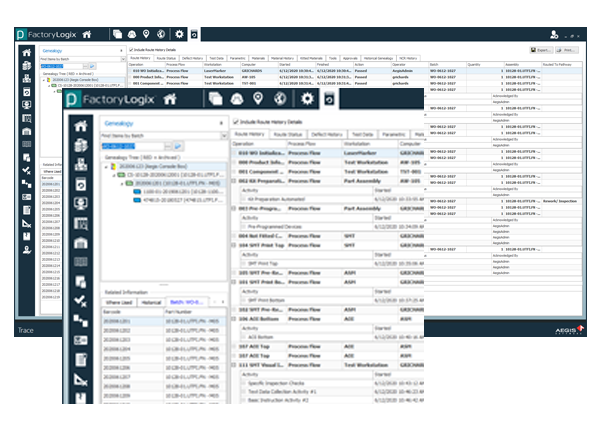
Product production process traceability

Quick release process

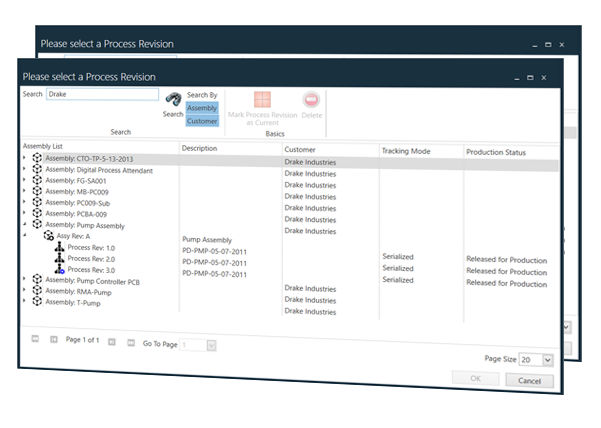
Core process does not leak

Centralization of data management
Other clients we helped.